Just-in-Time Access
Eliminate Standing Privileges, Not Productivity
Standing access is standing risk. Opal enforces time-bound, just-in-time access policies that eliminate excessive permissions without slowing anyone down. Access is requested through self-service workflows, evaluated against policy, and automatically revoked on expiration. No tickets. No stale roles. No attack surface you forgot about.

Just-in-Time Access
Eliminate Standing Privileges, Not Productivity
Standing access is standing risk. Opal enforces time-bound, just-in-time access policies that eliminate excessive permissions without slowing anyone down. Access is requested through self-service workflows, evaluated against policy, and automatically revoked on expiration. No tickets. No stale roles. No attack surface you forgot about.
Get a Demo
See the Platform

Just-in-Time Access
Eliminate Standing Privileges, Not Productivity
Standing access is standing risk. Opal enforces time-bound, just-in-time access policies that eliminate excessive permissions without slowing anyone down. Access is requested through self-service workflows, evaluated against policy, and automatically revoked on expiration. No tickets. No stale roles. No attack surface you forgot about.

Just-in-Time Access
Eliminate Standing Privileges, Not Productivity
Standing access is standing risk. Opal enforces time-bound, just-in-time access policies that eliminate excessive permissions without slowing anyone down. Access is requested through self-service workflows, evaluated against policy, and automatically revoked on expiration. No tickets. No stale roles. No attack surface you forgot about.

TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
The Problem
75% of Breaches Start With Over-Privileged Accounts
Your employees have access they haven't used in months. Service accounts run around the clock with admin privileges they need for five minutes. Every standing permission is a vulnerability — and traditional IAM can't close the gap fast enough.
10×
Average employee has 10× more access than required
67%
of access is never used after initial grant
$4.88M
Average cost of insider threat incidents
The Problem
75% of Breaches Start With Over-Privileged Accounts
Your employees have access they haven't used in months. Service accounts run around the clock with admin privileges they need for five minutes. Every standing permission is a vulnerability — and traditional IAM can't close the gap fast enough.
10×
Average employee has 10× more access than required
67%
of access is never used after initial grant
$4.88M
Average cost of insider threat incidents
The Problem
75% of Breaches Start With Over-Privileged Accounts
Your employees have access they haven't used in months. Service accounts run around the clock with admin privileges they need for five minutes. Every standing permission is a vulnerability — and traditional IAM can't close the gap fast enough.
10×
Average employee has 10× more access than required
67%
of access is never used after initial grant
$4.88M
Average cost of insider threat incidents
The Problem
75% of Breaches Start With Over-Privileged Accounts
Your employees have access they haven't used in months. Service accounts run around the clock with admin privileges they need for five minutes. Every standing permission is a vulnerability — and traditional IAM can't close the gap fast enough.
10×
Average employee has 10× more access than required
67%
of access is never used after initial grant
$4.88M
Average cost of insider threat incidents
How Opal Solves It
From "Just-in-Case" to Just-in-Time
Opal layers on top of your existing infrastructure — Okta, AWS, Google Workspace, and 50+ more — to transform static permissions into dynamic, time-bound access. Start with your most sensitive resources and expand from there. No rip-and-replace required.
Zero standing privileges for sensitive resources · Automatic expiration and revocation · One-click emergency access with full audit trail

Key Capabilities
1. Instant Implementation
Forget six-month IAM overhauls. Opal connects to your existing identity providers and infrastructure in hours, not months

1. Instant Implementation
Forget six-month IAM overhauls. Opal connects to your existing identity providers and infrastructure in hours, not months

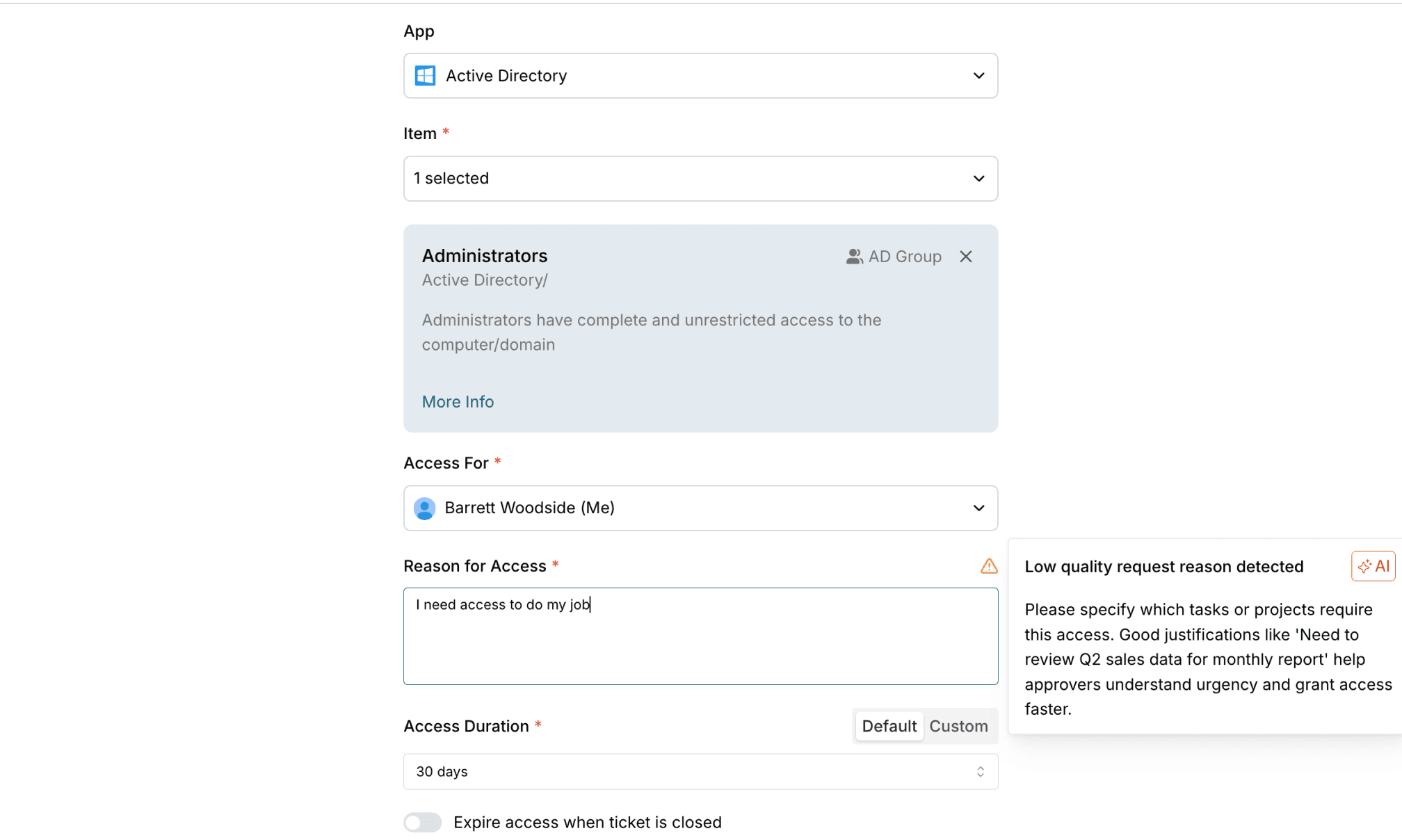
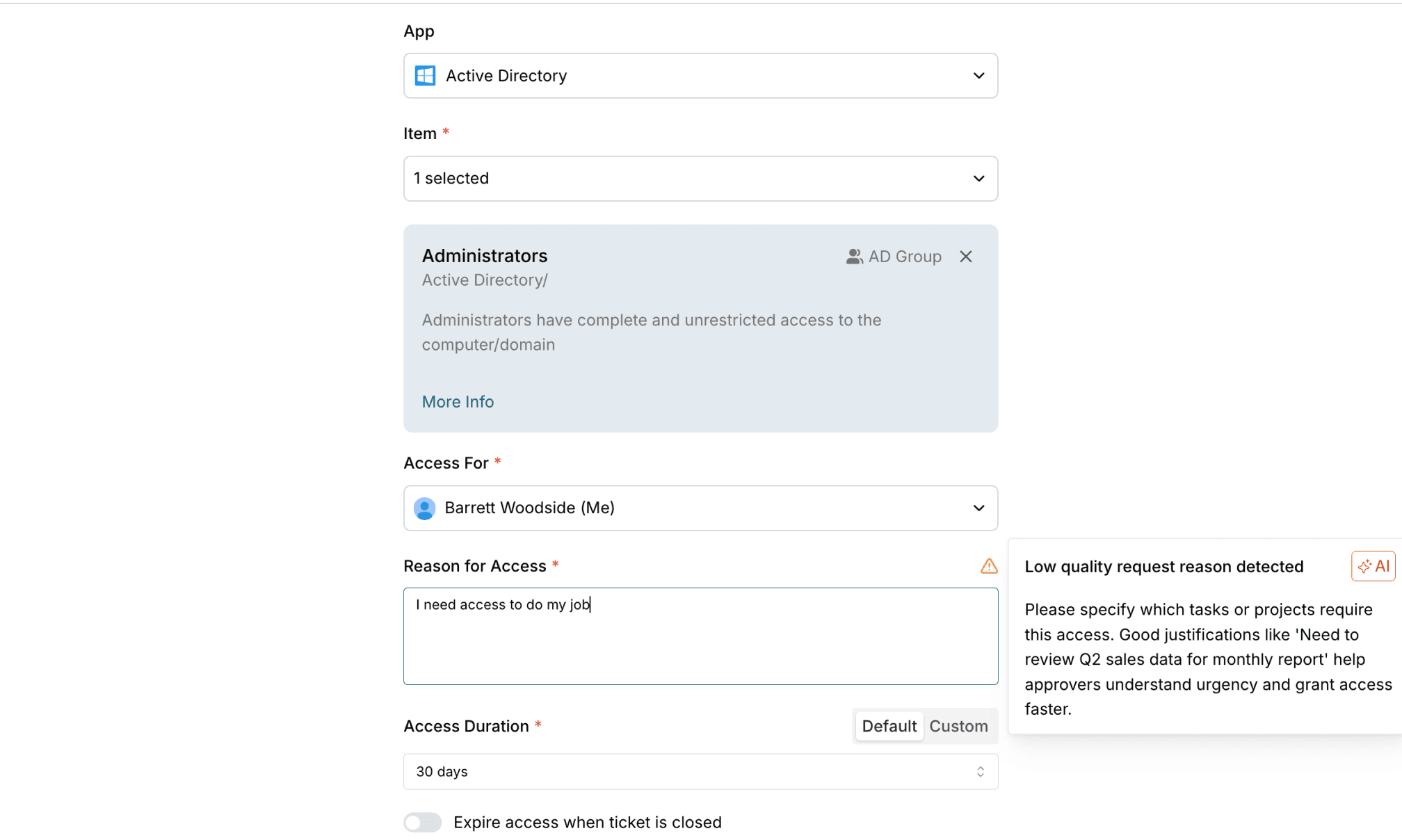
2. AI-Powered Request Evaluation
Opal's authorization reasoning engine goes beyond simple if/then logic. It understands who needs what, when they need it, and why — automatically routing approvals, suggesting access duration, and flagging anomalies before they become incidents.

2. AI-Powered Request Evaluation
Opal's authorization reasoning engine goes beyond simple if/then logic. It understands who needs what, when they need it, and why — automatically routing approvals, suggesting access duration, and flagging anomalies before they become incidents.

3. Security Without Friction
No more IT tickets gathering dust. No more productivity killed by "submit and wait." Opal's JIT access works where your teams already work, in Slack, Teams, or via direct API. Pre-approved requests execute instantly. Everything else gets smart-routed in seconds.

3. Security Without Friction
No more IT tickets gathering dust. No more productivity killed by "submit and wait." Opal's JIT access works where your teams already work, in Slack, Teams, or via direct API. Pre-approved requests execute instantly. Everything else gets smart-routed in seconds.

4. Continuous Risk Reduction
Every JIT policy you implement immediately reduces risk. Opal's live dashboard shows exactly how much exposure you're eliminating: by user, by resource, by department.
4. Continuous Risk Reduction
Every JIT policy you implement immediately reduces risk. Opal's live dashboard shows exactly how much exposure you're eliminating: by user, by resource, by department.
Beyond Basic JIT
Beyond Basic JIT
The Platform Advantage
The Platform Advantage
While others stop at time-based access, Opal keeps going. Layer on contextual controls, multi-party approvals, and continuous verification. Build a complete identity security posture that adapts as threats evolve.
OpalQuery operates against Opal's unified identity and access graph; users, resources, and groups from every connected system. A few examples:
Access intelligence
Express JIT rules, SoD constraints, and break-glass procedures as version-controlled code with OpalScript
AI-powered reviews
Query your full identity graph in natural language with OpalQuery to surface orphaned accounts, SoD conflicts, and over-provisioned roles
Just-in-time access
Paladin evaluates every request against identity context, access history, and peer norms — approving or escalating with specific reasoning
Agent identity governance
Govern AI agents under the same policy framework as human identities
Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story


5,353
Okta entitlements governed
How Mercari Built Zero-Touch Access to Production
See customer story


5,000
Employees secured
Blend Transforms Identity Security with Deterministic Logic
See customer story


150+
Apps under governance
Superhuman Reduced Access Risk While Improving End-User Experience
See customer story

Stop Managing Permissions. Start Managing Risk.
Identity security that's programmable, autonomous, and built for what's next. Join the security teams who've made standing privileges obsolete.
Stop Managing Permissions. Start Managing Risk.
Identity security that's programmable, autonomous, and built for what's next. Join the security teams who've made standing privileges obsolete.
Stop Managing Permissions. Start Managing Risk.
Identity security that's programmable, autonomous, and built for what's next. Join the security teams who've made standing privileges obsolete.
Stop Managing Permissions. Start Managing Risk.
Identity security that's programmable, autonomous, and built for what's next. Join the security teams who've made standing privileges obsolete.
Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.
