AI-Powered Access Reviews
Stop Rubber-Stamping. Start De-Risking.
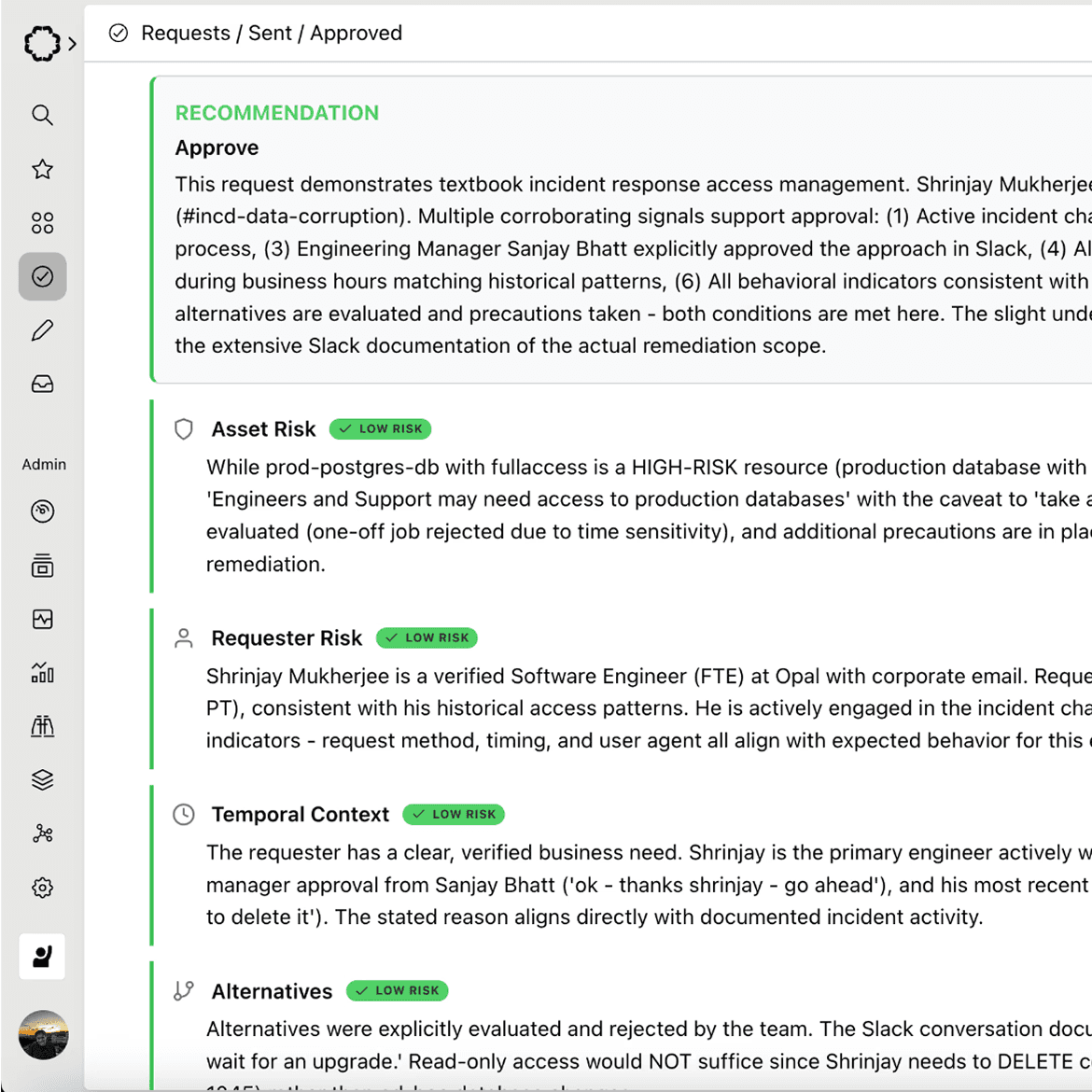
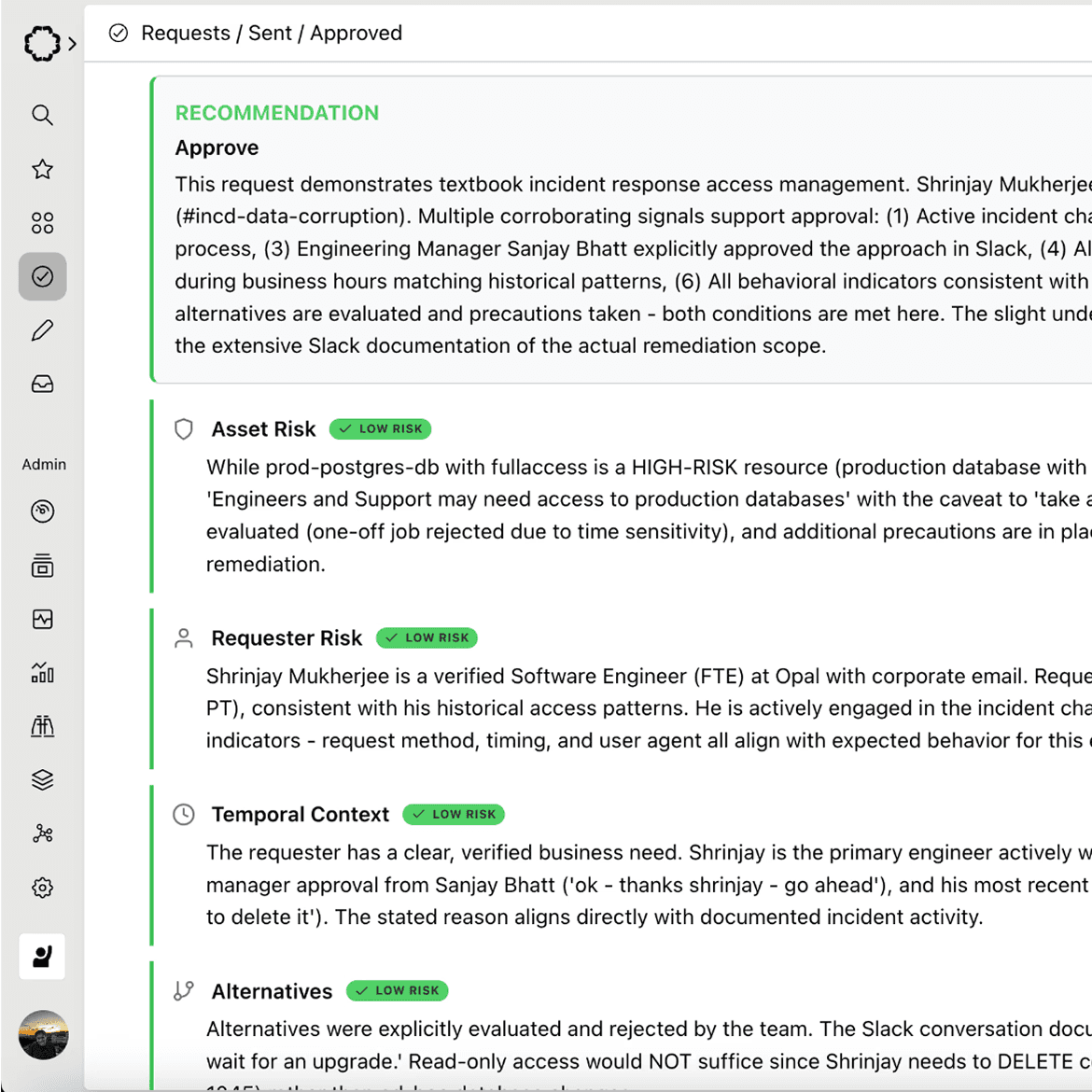
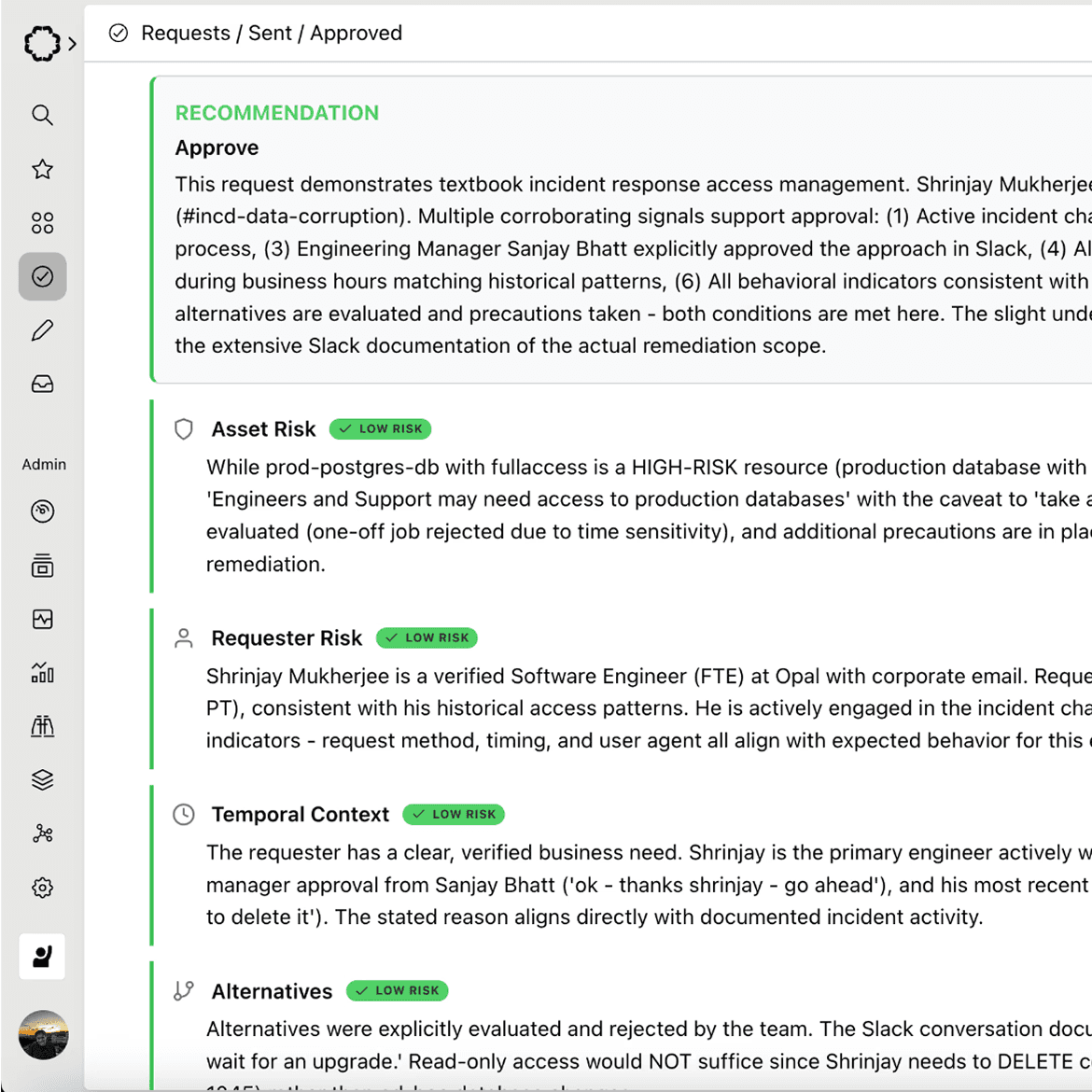
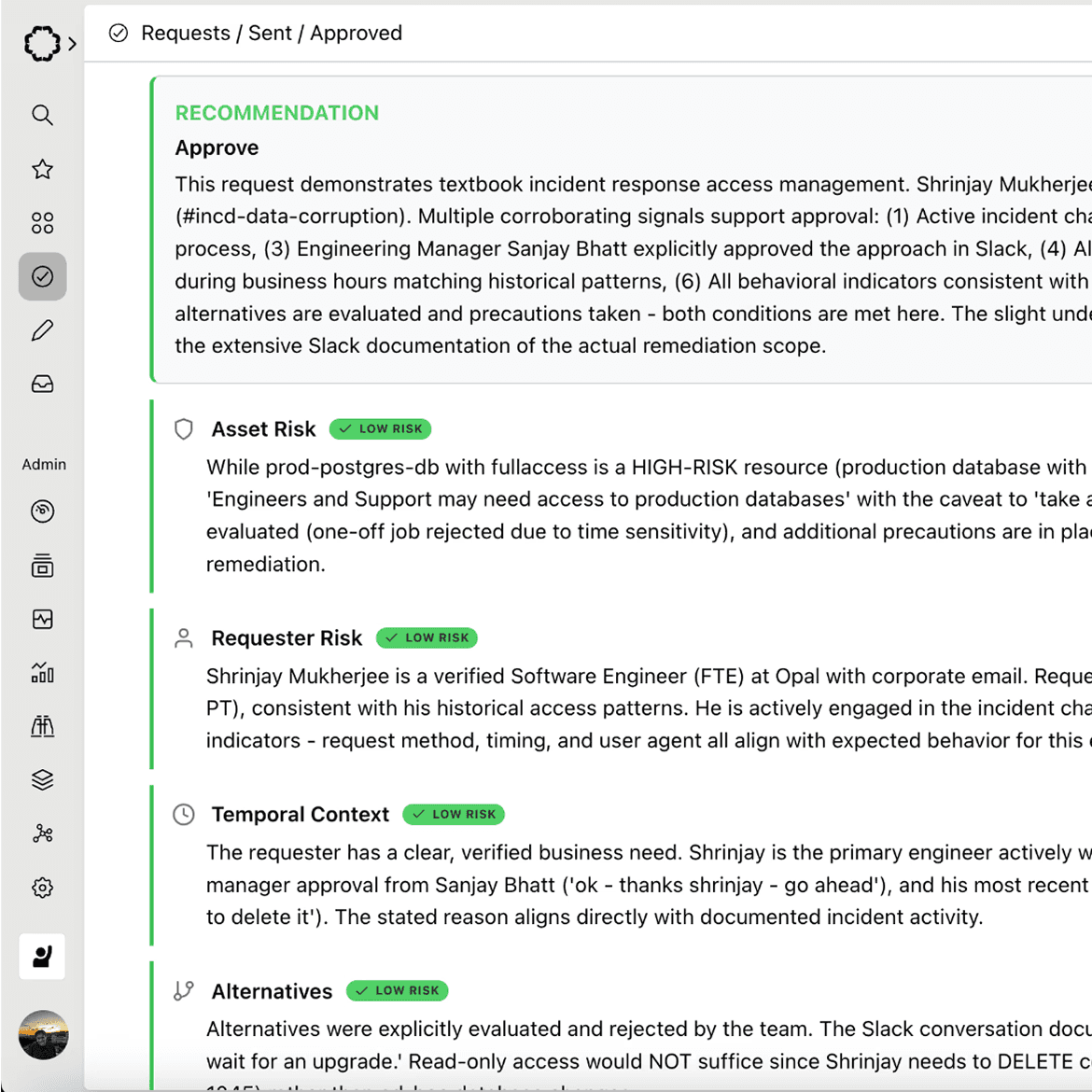
Access reviews are broken — not because reviewers don't care, but because they don't have context. Paladin operates as an AI-powered reviewer directly in Opal's approval chain, evaluating every request against identity context, access history, ticket references, resource sensitivity, and peer norms. It approves with confidence or escalates with specific reasoning. Decision time drops from hours to seconds. No rubber stamps. No reviewer fatigue. No risk hiding in a backlog.
AI-Powered Access Reviews
Stop Rubber-Stamping. Start De-Risking.
Access reviews are broken — not because reviewers don't care, but because they don't have context. Paladin operates as an AI-powered reviewer directly in Opal's approval chain, evaluating every request against identity context, access history, ticket references, resource sensitivity, and peer norms. It approves with confidence or escalates with specific reasoning. Decision time drops from hours to seconds. No rubber stamps. No reviewer fatigue. No risk hiding in a backlog.
AI-Powered Access Reviews
Stop Rubber-Stamping. Start De-Risking.
Access reviews are broken — not because reviewers don't care, but because they don't have context. Paladin operates as an AI-powered reviewer directly in Opal's approval chain, evaluating every request against identity context, access history, ticket references, resource sensitivity, and peer norms. It approves with confidence or escalates with specific reasoning. Decision time drops from hours to seconds. No rubber stamps. No reviewer fatigue. No risk hiding in a backlog.
AI-Powered Access Reviews
Stop Rubber-Stamping. Start De-Risking.
Access reviews are broken — not because reviewers don't care, but because they don't have context. Paladin operates as an AI-powered reviewer directly in Opal's approval chain, evaluating every request against identity context, access history, ticket references, resource sensitivity, and peer norms. It approves with confidence or escalates with specific reasoning. Decision time drops from hours to seconds. No rubber stamps. No reviewer fatigue. No risk hiding in a backlog.
Get a Demo
See the Platform
TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
TRUSTED BY LEADING COMPANIES
The Problem
Manual Reviews Don't Scale — and Attackers Know It
Quarterly access reviews were designed for a slower world. Today, security teams face thousands of entitlements across hundreds of systems, and the review process hasn't changed: a spreadsheet lands in a manager's inbox, they approve everything because they lack context to do otherwise, and the cycle repeats. Meanwhile, over-provisioned accounts sit untouched for months — exactly the kind of standing risk attackers exploit.
83%
of access review decisions are approved without meaningful evaluation
6+ hours
average time for a reviewer to complete a single certification campaign
Quarterly
the cadence most teams rely on — leaving 90 days of unmanaged drift between cycles
The Problem
Manual Reviews Don't Scale — and Attackers Know It
Quarterly access reviews were designed for a slower world. Today, security teams face thousands of entitlements across hundreds of systems, and the review process hasn't changed: a spreadsheet lands in a manager's inbox, they approve everything because they lack context to do otherwise, and the cycle repeats. Meanwhile, over-provisioned accounts sit untouched for months — exactly the kind of standing risk attackers exploit.
83%
of access review decisions are approved without meaningful evaluation
6+ hours
average time for a reviewer to complete a single certification campaign
Quarterly
the cadence most teams rely on — leaving 90 days of unmanaged drift between cycles
The Problem
Manual Reviews Don't Scale — and Attackers Know It
Quarterly access reviews were designed for a slower world. Today, security teams face thousands of entitlements across hundreds of systems, and the review process hasn't changed: a spreadsheet lands in a manager's inbox, they approve everything because they lack context to do otherwise, and the cycle repeats. Meanwhile, over-provisioned accounts sit untouched for months — exactly the kind of standing risk attackers exploit.
83%
of access review decisions are approved without meaningful evaluation
6+ hours
average time for a reviewer to complete a single certification campaign
Quarterly
the cadence most teams rely on — leaving 90 days of unmanaged drift between cycles
The Problem
Manual Reviews Don't Scale — and Attackers Know It
Quarterly access reviews were designed for a slower world. Today, security teams face thousands of entitlements across hundreds of systems, and the review process hasn't changed: a spreadsheet lands in a manager's inbox, they approve everything because they lack context to do otherwise, and the cycle repeats. Meanwhile, over-provisioned accounts sit untouched for months — exactly the kind of standing risk attackers exploit.
83%
of access review decisions are approved without meaningful evaluation
6+ hours
average time for a reviewer to complete a single certification campaign
Quarterly
the cadence most teams rely on — leaving 90 days of unmanaged drift between cycles
How Opal Solves It
From Rubber Stamp to Rigorous Evaluation
From Rubber Stamp to Rigorous Evaluation Paladin doesn't replace human reviewers — it gives them superpowers. Every access request passes through Paladin's evaluation engine before a human ever sees it. High-confidence decisions are resolved instantly. Ambiguous or high-risk requests are escalated with a full investigation summary, so reviewers act on Paladin's analysis instead of starting from scratch. The result: faster decisions, fewer errors, and reviews that actually reduce risk.
AI-powered evaluation of every request · Instant resolution of routine approvals · Escalation with reasoning for high-risk decisions

Key Capabilities
1. Contextual Evaluation at Machine Speed
Paladin evaluates every access request against the signals that matter: who is requesting, what they're requesting access to, whether a ticket or justification supports it, how sensitive the resource is, and what their peers typically have. This isn't pattern matching — it's the investigation a senior security engineer would do, executed in seconds.
1. Contextual Evaluation at Machine Speed
Paladin evaluates every access request against the signals that matter: who is requesting, what they're requesting access to, whether a ticket or justification supports it, how sensitive the resource is, and what their peers typically have. This isn't pattern matching — it's the investigation a senior security engineer would do, executed in seconds.
2. First-Class Reviewer in the Approval Chain
Paladin isn't a sidecar or a recommendation engine — it operates as a first-class reviewer within Opal's approval workflows. It can approve, deny, or escalate based on OpalScript-defined policy. When it escalates, it provides specific, actionable reasoning — not a risk score, but a narrative: what it found, what concerned it, and what the human reviewer should focus on.

2. First-Class Reviewer in the Approval Chain
Paladin isn't a sidecar or a recommendation engine — it operates as a first-class reviewer within Opal's approval workflows. It can approve, deny, or escalate based on OpalScript-defined policy. When it escalates, it provides specific, actionable reasoning — not a risk score, but a narrative: what it found, what concerned it, and what the human reviewer should focus on.

3. Continuous Review, Not Quarterly Campaigns
Access reviews shouldn't be a quarterly fire drill. Paladin monitors the access graph continuously, evaluating entitlements as they're granted and flagging drift as it happens. When an entitlement no longer aligns with policy, peer norms, or business need, Paladin surfaces it immediately — not three months from now.

3. Continuous Review, Not Quarterly Campaigns
Access reviews shouldn't be a quarterly fire drill. Paladin monitors the access graph continuously, evaluating entitlements as they're granted and flagging drift as it happens. When an entitlement no longer aligns with policy, peer norms, or business need, Paladin surfaces it immediately — not three months from now.

4. Measurable Risk Reduction
Every decision Paladin makes is auditable, traceable to policy, and measurable. Security teams can quantify exactly how much reviewer burden Paladin absorbs, how many high-risk escalations it surfaces, and how review completion times change — giving leadership the data to prove that access reviews are actually reducing risk, not just checking a box.

4. Measurable Risk Reduction
Every decision Paladin makes is auditable, traceable to policy, and measurable. Security teams can quantify exactly how much reviewer burden Paladin absorbs, how many high-risk escalations it surfaces, and how review completion times change — giving leadership the data to prove that access reviews are actually reducing risk, not just checking a box.

Impact
Beyond Access Reviews
Beyond Access Reviews
The Platform Advantage
The Platform Advantage
Paladin is powerful on its own, but it's transformative as part of Opal's See → Encode → Enforce loop. The policies Paladin enforces are authored in OpalScript. The identity context it evaluates comes from OpalQuery. And every decision it makes feeds back into the access graph, sharpening future evaluations.
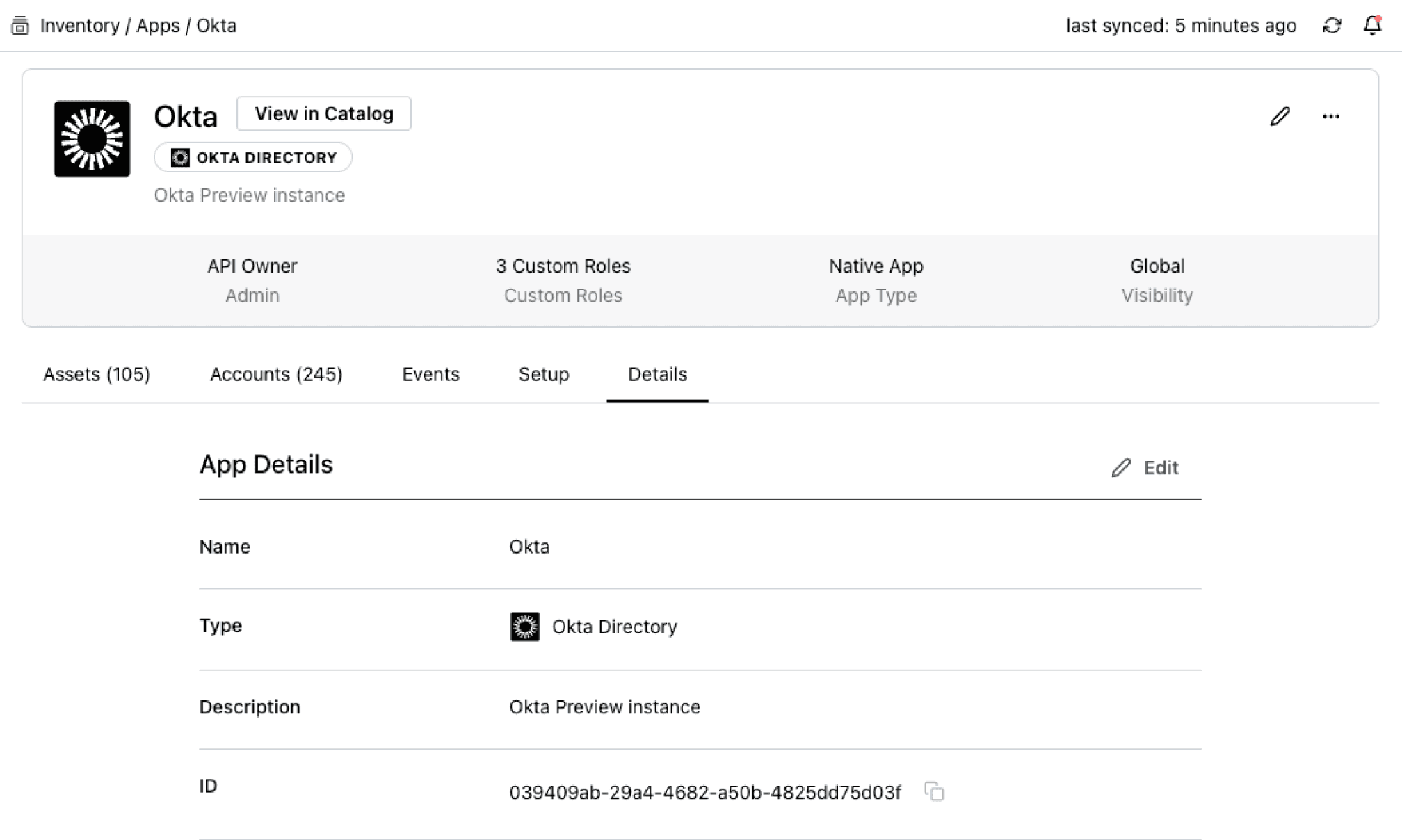
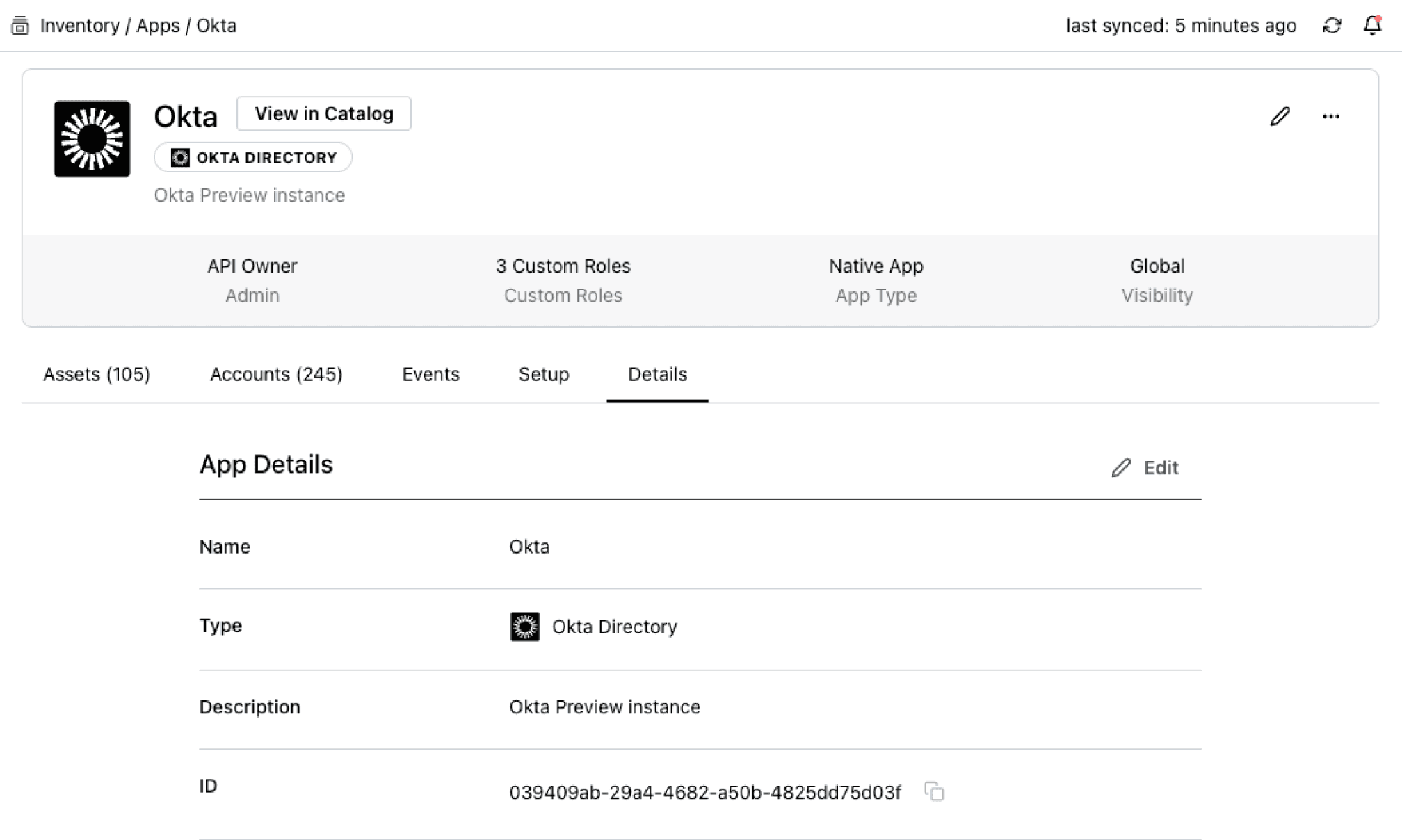
OpalQuery operates against Opal's unified identity and access graph; users, resources, and groups from every connected system. A few examples:
Access intelligence
OpalQuery gives Paladin (and your team) the full identity graph to evaluate requests against: entitlements, peer norms, SoD conflicts, and resource sensitivity
AI-powered reviews
OpalScript defines the policies Paladin enforces — approval chains, escalation criteria, auto-approval thresholds — all as version-controlled, testable code
Just-in-time access
Paladin-approved access is time-bound by default, eliminating standing privileges even when requests are approved
Agent identity governance
Paladin evaluates non-human identities — AI agents, service accounts, automation credentials — under the same framework as human access
Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story


5,353
Okta entitlements governed
How Mercari Built Zero-Touch Access to Production
See customer story


5,000
Employees secured
Blend Transforms Identity Security with Deterministic Logic
See customer story


150+
Apps under governance
Superhuman Reduced Access Risk While Improving End-User Experience
See customer story

Trusted by security teams that ship fast and sleep well.

86K
Time-bound access requests
JIT Access and UARs Enhance Productivity and Security at Databricks
See customer story




Access Reviews That Actually Reduce Risk
Identity security that's programmable, autonomous, and built for what's next. Replace the quarterly fire drill with continuous, AI-powered evaluation that scales with your business.
Access Reviews That Actually Reduce Risk
Identity security that's programmable, autonomous, and built for what's next. Replace the quarterly fire drill with continuous, AI-powered evaluation that scales with your business.
Access Reviews That Actually Reduce Risk
Identity security that's programmable, autonomous, and built for what's next. Replace the quarterly fire drill with continuous, AI-powered evaluation that scales with your business.
Access Reviews That Actually Reduce Risk
Identity security that's programmable, autonomous, and built for what's next. Replace the quarterly fire drill with continuous, AI-powered evaluation that scales with your business.
Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.

Stop Reviewing.
Start Enforcing.
